It’s been a while but as I have just stuggled with integrating a UPS into HASS, I thought I’d write a few words about it. If you like, you can skip the semi ranting paragraph below and jump to “And here we are”.
I have been hooked on Home Assistant for some time now and almost every single light in my house is smart connected. While that have lots and lots of advantages, there are a few disadvantages. Having software running in each light bulb means that light bulbs will crash (as in going off line, not as in getting shattered). Occasionally a light will not respond but after a quick reboot (sigh) it will be back on line. That reboot comes from me flicking the “old” light switches and the lights turning on after a mains power failure (a “feature”).
You might see where this is going. Twice this winter I have been rather rudely woken up at night when a power grid glitch caused a total of 3000 lux flooding my bedroom. I then need to rise from bed, manually turn off bunch of lights or await the HASS server reboot and turn the lights off from the comfort of my bed.
Of course it should not have to be this way. What if…lights at boot went back to the previous setting? Well, as the lights are radio connected, disturbances will happen from time to time and I am quite certain the software glitches too so the “lights on at power on” setting is needed. Crappy technology and buggy software that cannot be fixed need…work arounds.
And here we are
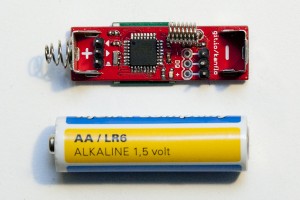
So I purchased a PowerWalker VI 600-3000 SCL to keep the HASS server alive during power grid glitches and blackouts. Integration was not straight forward. In case you want to do the same, here are my notes.
NUT add-on
First install the “NUT add-on”. Yes, add-on, not integration (that comes later). The “add-on” creates the server that the “integration” talks to. Go to “Settings > Add-ons” and search for Network UPS Tools or NUT. Next go to the NUT “Configuration” section. You need to define a user, UPS name and select a driver for your UPS. The driver for my UPS is called nutdrv_qx. While it enumerated as a USB HID device, selecting “HID” as driver at first threw me down the rabbit hole, wasting an entire evening of googling “NUT libusb permissions”. Pick nutdrv_qx and save time. Oh! And make sure to disable shutdown_host!
Now go back to the “Info” section and start the add-on. Checking the logs, the last line should be something like
0.010152 [D1] Logged into UPS PowerWalker@localhost
I did experience the NUT service restarting every 10 seconds. It went away and I cannot explain what I did.
NUT integration
Go to “Settings > Devices & services”. Chances are the “NUT add-on” has been helpfully auto discovered. If so, dismiss it. Click “Add integration” and add the NUT integration. Specify a0d7b954-nut as host name and the user/password from the add-on configuration. Oddly, the auto discovered integration did not accept my credentials. Might have been a typo on my behalf. YMMW.
Next I need some UPS automation, but that is for another evening.
Final Notes
In case of a power outage, my UPS will beep every ten seconds which would probably be more of an impediment to a good night’s sleep than the 3000 lux blast I am trying to mitigate. Luckily it can be turned off, via another Linux box. Install the NUT toolkit with sudo apt install nut and run the command upsc PowerWalker@homeassistant.local. Enter the credentials from the NUT add-on (PowerWalker is the name given in the devices section of the add-on configuration).
Next check the settings using the command upsc PowerWalker@homeassistant.local. Somewhere you should see ups.beeper.status: enabled. Disable with the command upscmd PowerWalker@homeassistant.local beeper.toggle. It seems it takes a few seconds for the setting to persist.
If you have another UPS that I do, you can check the supported commands using the command upscmd -l PowerWalker@homeassistant.local.
Slava Ukraini!